You might have already heard that the internet is teeming with a lot of bad eggs that just want to either get a hold of you and your website’s information, or just be there to ruin your day. Nevertheless, it’s never a fun experience to go through when you’re hacked.
Whether it’s your smartphone, your computer, your files, or worst, your business website, it’s one of the most frustrating things to go through.
That said, it’s not the end of the world. As with anything bad, prevention is better than cure, but a cure won’t hurt either in case you’re already there.
In this article, we’ve listed a couple of recommendations and steps on how to handle and fix a hacked website. Whether you’re a beginner or a pro, you’re bound to make use of the information we provide.
If you’re in a rush, here’s a quick glance on what you’re looking at when taking care of your hacked WordPress site.
| Plugin | Time Required To Fix Hacked Site | Start Cost | Money-Back Guarantee |
|---|---|---|---|
| MalCare | 12 hours | $99 per year | Yes, 300% money back for manual cleanup by security analyst |
| Sucuri | 6 hours guaranteed response | $199 per year | Yes, 30-day money-back guarantee |
| WordFence | Depends, no guaranteed time given | $179 plus 200$ if you expedite the order. | No, but they offer 90 days work guarantee if post-service recommendations are followed |
| Do-it-Yourself (DIY) | 24 hours + | $0 | None |
Professional Third-Party Services
WordPress is easy to use and that’s why it attracts millions of non-tech savvy users every day. In fact it powers more than a third of the whole internet.
So, when a site is hacked, not many users have the technical knowledge to cope with the situation. Also, businesses using WordPress need to figure out a quick way to fix their site. Failing that, they will start losing revenue. To ensure that it doesn’t happen, your WordPress site needs immediate attention from professionals.
To help you make a choice, we have listed three popular and reliable professional services that get the job done for you: MalCare, Sucuri, and WordFence.
1. MalCare

MalCare is one of the leading WordPress security service providers out there. They offer their services through their WordPress security plugin and a team of professional security experts.
The plans start from $99 per year per site. Once you purchase their basic plan, you need to install the MalCare plugin as it automatically scans and fixes your site. All you need to do is run the one-click malware scan and fix service from the dashboard and sit back and relax as it gets rid of the infected files and services.
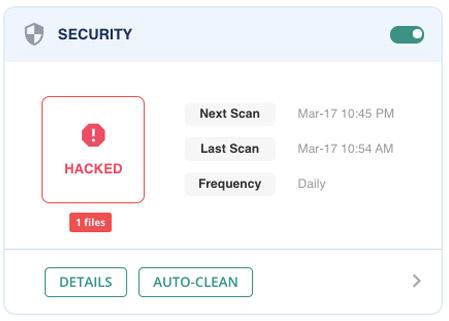
If the automatic cleanup service fails to fix your site, you can connect with their support team and provide them the login details in the form of FTP, SFTP, or SSH. They will go through your site and fix it before handing it back to you.
Not everyone can wait for their site to get fixed, and that’s where the Emergency Malware Cleanup service at $249 comes in. Their team of security experts will ensure the malware is removed from your website in under 12 hours. If they are not able to remove the malware, they will offer a 300% money-back guarantee!
How It Works
All you need to do is provide the MalCare team the login details of your website and follow the steps below:
- Get in touch from here and choose a plan according to your budget and requirement.
- Submit website details for your hacked website. They need access to your site in the form of SSH, SFTP, and FTP. You can connect with your hosting provider for the details.
- Their security analyst will clean the site.
Once the site is cleaned, they will contact you with a detailed report.
Pros
- MalCare is cheaper compared to other solutions.
- The website is cleaned within 12 hours if you use their Emergency Malware Cleanup.
- No limitations on the size of your website or type of malware.
- Their MalCare plugin offers an auto-clean malware option.
- It is easy to set up and run.
- It scans and cleans sites quickly through an automated process.
- The plugin also offers unlimited scans.
Cons
- The UI of their dashboard is quite outdated.
MalCare is an easy-to-use professional solution that you can use if your site gets hacked. It offers both emergency cleanup services and plugin-based solutions
2. Sucuri
Sucuri offers a complete security solution for the WordPress platform. They offer WordPress security services through their plugin which helps you to harden your site. Apart from that, they also have a team of security experts that helps you to fix your hacked site.
You can pick any of the available plans on their site to get started. Their basic plans start at $199 per year. The plan doesn’t have any guaranteed service-level agreement (SLA) but you can expect approximately 24-72 hours for them to clean your site.
However, If you’re in need of immediate cleanup, then you can choose the business plan which costs $499 per year as it comes with 6 hours guaranteed SLA. This means your site will be fixed within six hours of you submitting your malware-removal request.
Their last plan is the PRO plan at $299.99 per year. The difference between the basic plan and the PRO version is the malware and scan frequency which stands at 12 hours and 6 hours respectively. The business plan, on the other hand, is the only plan that offers guaranteed SLA and a malware and scan frequency of 30 mins.
All of their plans come with a 30-day money-back guarantee.
How It Works
So, how does it work? Let’s check out the steps below.
- Go here and choose one of their plans according to your budget and urgency.
- Create an account and buy that plan.
- Create a malware removal request and submit the necessary login information.
With each of the plans, you can expect them to do the following:
- Identify security issues on your site.
- Repair the issues and provide you a complete service report.
Pros
- One of the most comprehensive security solutions.
- Sucuri hardens your site so that your site becomes more secure.
- All their plans come with 30-days money-back guarantee.
- Runs scanning and firewall through their cloud security platform.
Cons
- Costlier compared to other solutions if you want your site fixed as early as possible.
Sucuri is undoubtedly one of the best security solutions for WordPress sites. Their professional team is capable of fixing hacked sites with guaranteed results. Apart from that, their plugin ensures your site is more secure and safe from future hacks.
3. WordFence
WordFence is a well known WordPress security plugin. Its popularity can be gauged by the fact that it has over 3+ million active installations for their free plugin.
However, WordFence works differently compared to Sucuri as it runs all its tasks on your WordPress site server.
When it comes to fixing hacked WordPress sites, they offer their complete WordPress Site Cleaning Service for $179 per site. By purchasing their service, you also get their one-year premium WordFence premium license which costs $99 per year if bought separately.
At the time of writing, they are charging twice due to increased demand. This means, when the demand is low, you can get their service for just $179.
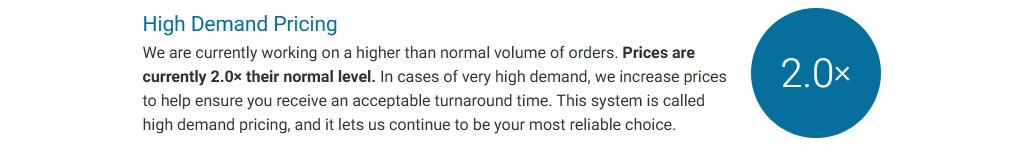
They also have an “expedite” option during the checkout. The “expedite my order” option is for website owners running mission-critical services. If you choose the option, you need to pay $100 more per order (price changes depending on demand).
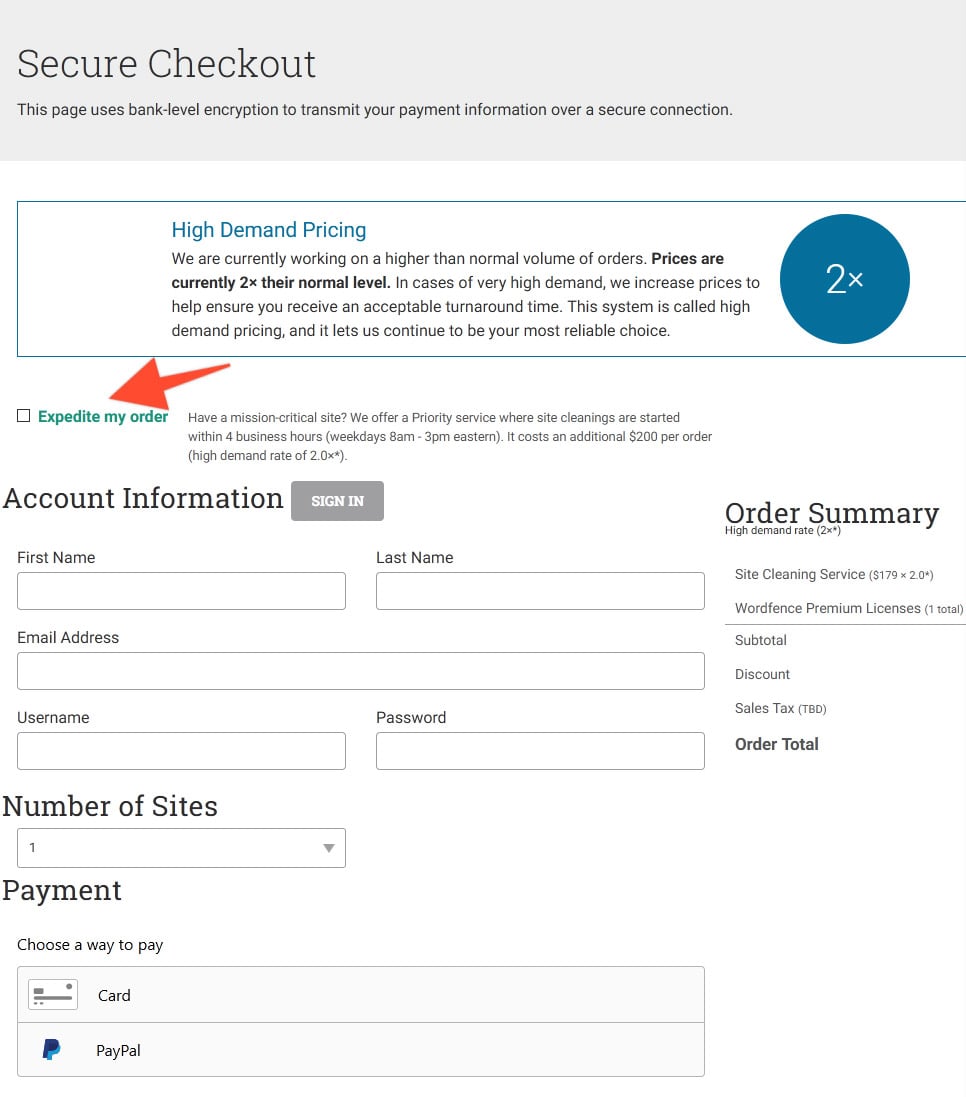
In total, it can cost you anywhere between $179 to $700 (or even more) for using their professional services.
In case their prices are hiked due to demand, you can check out other security solution providers such as MalCare and Sucuri which do not use the pricing model based on demand.
How It Works
To get started, you need to buy their Complete WordPress Site Cleaning Services first. You can do so by checking the link here.
Once done, you need to submit the FTP, SFTP, or SSH login information to them via their site.
WordFence follows a six-step process:
- Clean the infection
- Analyze how the attackers gained entry to the site
- Remove any malicious links and code from source code, pages, posts and comments
- Provides an infection removal and in-depth investigation report
- Remove your site from blacklist
- Provide a detailed checklist to secure your site from future attacks
They also offer 90 days of service guarantee if you follow their post-service recommendation.
Pros
- WordFence is a comprehensive WordPress security plugin
- They offer good on-boarding process
- Offers a detailed checklist to secure their site after your site gets fixed
- Their plugin helps you harden your site afterward
- WordFence Premium comes bundled within their WordPress Site Cleaning Service
Cons
- Pricing is not constant
- Their plans for fixing hacked sites can be costly depending on the high demand pricing multiplier
WordFence offers good cleanup services for hacked sites. Their free plugin is also generous when it comes to features. However, their pricing model for emergency services can be improved to better serve their customers.
Do It Yourself (DIY)
If you are relatively tech-savvy or don’t have the budget to take any of the above professional services, then you can also try to fix your hacked WordPress site yourself.
In this section, we will go through a series of steps that will let you identify and clean your hack. We will also cover the post hack list, which will enable you to protect your site from future hacks.
So, let’s get started.
Things to Do Before Starting With DIY
Most hosting providers delete hacked sites from their servers as soon as they come to know about it. They do it to ensure that other sites on the server do not get infected.
That’s why you should back up your site once you have determined that your site has been hacked.
Most hosting providers have their own backup system, so you can use it to restore your site. However, if you do not have backups from your hosting, you might want to connect with them and learn what can be done.
In short, you need to make sure that you take a complete backup of your site including its database and files.
With your site backed up, you can peacefully move on to fixing your hacked site.
In case, if you have a backup of your previous, clean site, you can restore it. And, then follow our checklist so this clean site from your backup won’t get hacked.
After that, you can harden your site by following the post hack recommendation we shared below.
Let’s move on to the three key steps of fixing your hacked WordPress site by yourself.
1. Identifying the Hack
The first task is to identify the hack on your site. There are many tools that you can use to scan your site. For example, you can use Sucuri’s SiteCheck to do an external malware scan.
If the site is infected, then the scan will reveal it by showing a message. If the message doesn’t reveal enough information, then you need to do further checks. Start by asking these questions:
- Are you able to get into your WordPress dashboard?
- Has Google marked your site as insecure?
- Is your site redirecting to another site?
- Are there illegitimate links on your site?
Once you have answers to all these questions, make sure that you note all of them down as it will help you identify the hack or explain it to others if needed.
You can also use Google Transparency Report. It is a quick and easy way to determine if your site has been hacked and learn what’s wrong with it.
If your site is hacked, then it will return information about spam, downloads, and malicious redirects. It will also showcase if your site has any recent malware infection or not through the malware recent Google scan.
There are other checks that you need to do to learn about the hack. Those checks include the following.
- Core WordPress File Integrity Check
- Recently Modified Files Check
Core WordPress File Integrity Check
Here, you need to see if the core WordPress files are modified or not. To do so, you need to do an integrity check on three core folders, wp-includes, wp-admin, and root folders.
You can install the Sucuri plugin to do a core integrity check. Every time, you open the Sucuri dashboard, it scans the core WordPress files. If any change is detected, it will list the infected files with the status. In the “choose the action” option, you can either restore the file or delete it from your installation.
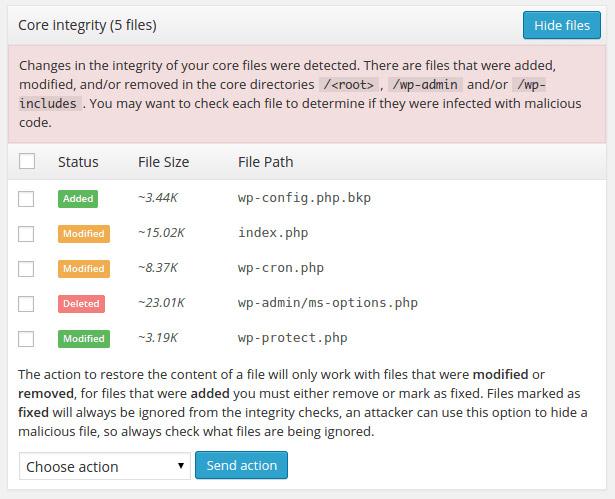
WordFence is also good when it comes to identifying and checking core WordPress file integrity.
If for some reason, you are not able to open the WordPress dashboard, then you need to use the terminal to check core integrity.
The best way to do so is to use the terminal to connect to the server and then use the diff command to check the difference between your WordPress files and original WordPress core files.
If you are not sure how the diff command works, then check out the detailed tutorial on it here: Diff Command in Linux. Another way is to use SFTP and manually check the files.
If you are not familiar with the terminal, then check out the terminal for beginners’ guide.
The key here is to check for any file changes. If there is no modification of any sort, then your site’s core files are clean and you need to look for infection somewhere else.
Recently Modified Files Check
Apart from the core WordPress files, you need to also check for any modified themes or plugins that you have on your site. You may also want to check /uploads/ directory for any modified files.
To do so, you can either manually check for modified files using Secure Shell (SSH) command or use the terminal command on Linux.
Not sure how to use FTP? Check out the FTP tutorial here. For SSH, check out this tutorial.
Using SSH
- First, you need to login to your server using SSH terminal or FTP client.
- Once done, you need to use the following command to check for the modified files for the past 21 days.
$ find ./ -type f -mtime -21
Using Linux Terminal
You need to use the following command in your terminal.
$ find /etc -type f -printf ‘%TY-%Tm-%Td %TT %p\n’ | sort -r.
In case you want to check directory files, then you need to use a slightly modified command.
$ find /etc -printf ‘%TY-%Tm-%Td %TT %p\n’ | sort -r.
Once you found out about the modified files, simply replace them with their fresh copies.
2. Cleaning the Hack
Now that we have thoroughly checked the site for changes, modifications, and infections, it is now time to clean the site.
Manually Removing the Malware Infection
To manually remove malware infection, you need to replace infected files with their fresh copies. In case your core WordPress files are modified or infected, you can replace them manually. To do so, you need to use an FTP client and simply overwrite new files over the existing ones. We recommend FileZilla — an easy to use FTP client with an excellent user interface.
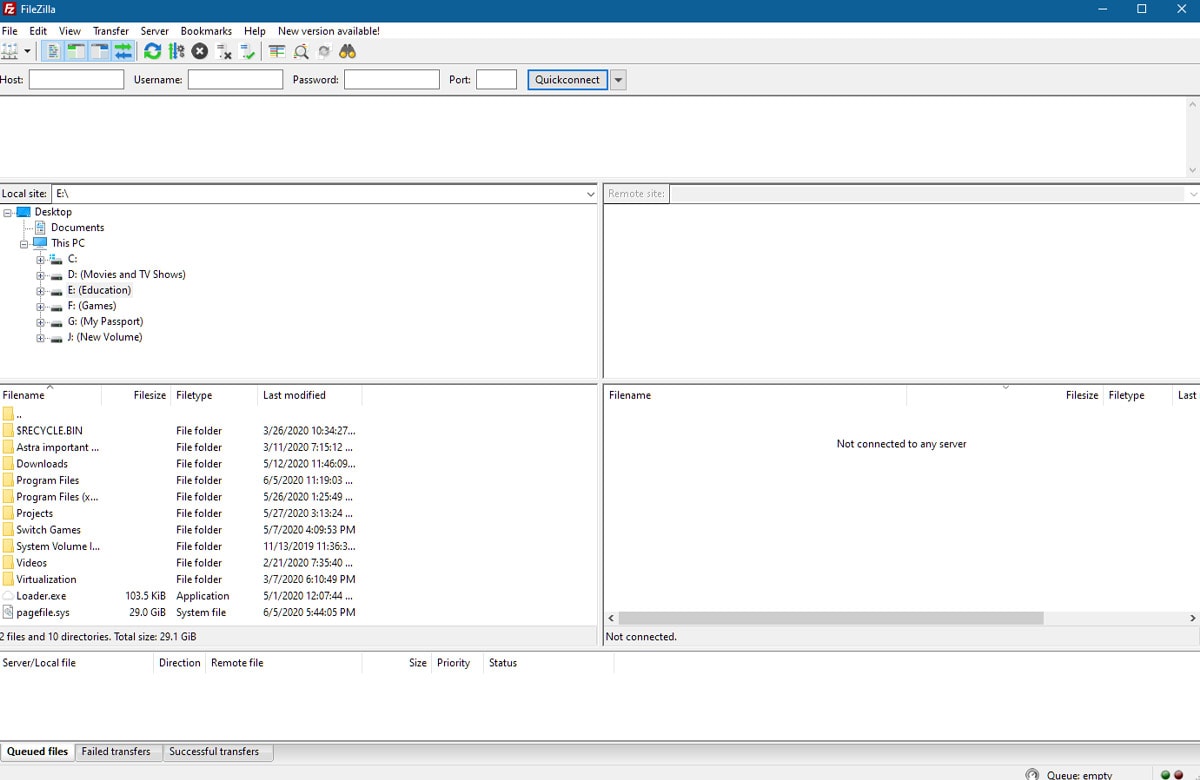
Before you start replacing the core files, make sure that you do not overwrite the wp-content folder and wp-config.php file.
But, what about the custom files? For custom files, you need to use your recent backups as a source for it. If you do not have a backup, then you need to scan the custom files using a malware scanner provided by Sucuri, WordFence or MalCare.
Finally, you need to remove any suspicious files.
Also, if you are not confident in what you are doing, it is always best to leave it to professionals and go for their services.
Cleaning Hacked Database Tables
In this step, you need to manually remove a suspicious malware infection from your database tables.
Those who are new to WordPress can use information from the malware scanner to clean the database tables. So, if the malware scanner shows infection in a particular table, then you need to clean it up. This requires you to have access to the database admin panel.
You also need to search for suspicious information yourself and manually remove them.
To make the process of cleaning up hacked database tables easier, you can use tools such as Adminer or Search-Replace-DB.
Securing User Accounts
In this step, we will show you how to secure user accounts. It is common for hacked websites to have unfamiliar user accounts. Hackers sometimes create an account in the WordPress admin area so that they can log in to the backend. It serves as a backdoor and can be used by the hacker even after you clean your site from the malware infection.
To make sure that it doesn’t happen, you need to secure your user accounts.
To do so, you need to go to your site backend and then click on Users >> All Users as shown below.
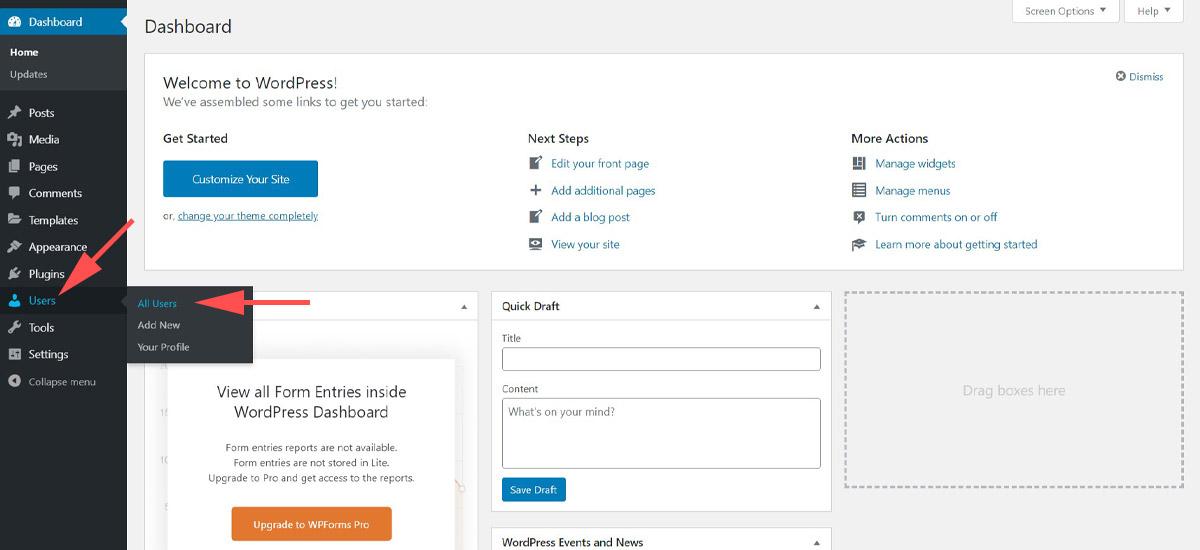
Now, you will see the whole list of users with different permissions. Take a look at them and if you find any unknown user, then delete it.
One more thing that you need to make sure that you are the only person with admin privileges.
Remove Hidden Backdoors in Your WordPress Site
Hackers usually leave a backdoor on the server when they hack a website. It allows them to access files on the server and make any changes to them.
Usually, hackers name the backdoor files in a way so they don’t look suspicious.
For example, in one of the recent attacks we saw, hackers had named the backdoor file as wp-xmlrpc.php in and it was uploaded in the root installation of WordPress. WordPress out of the box comes with a xmlrpc.php file. So this hacker smartly named his backdoor wp-xmlrpc.php so it does not look suspicious to naked eyes.
So as we discussed previously, you can find recently modified files and see if any of them is a backdoor.
3. Post Hack
Congratulations! You have successfully cleaned your site.
However, there are still steps that you need to do to ensure that another hack doesn’t happen in the near future.
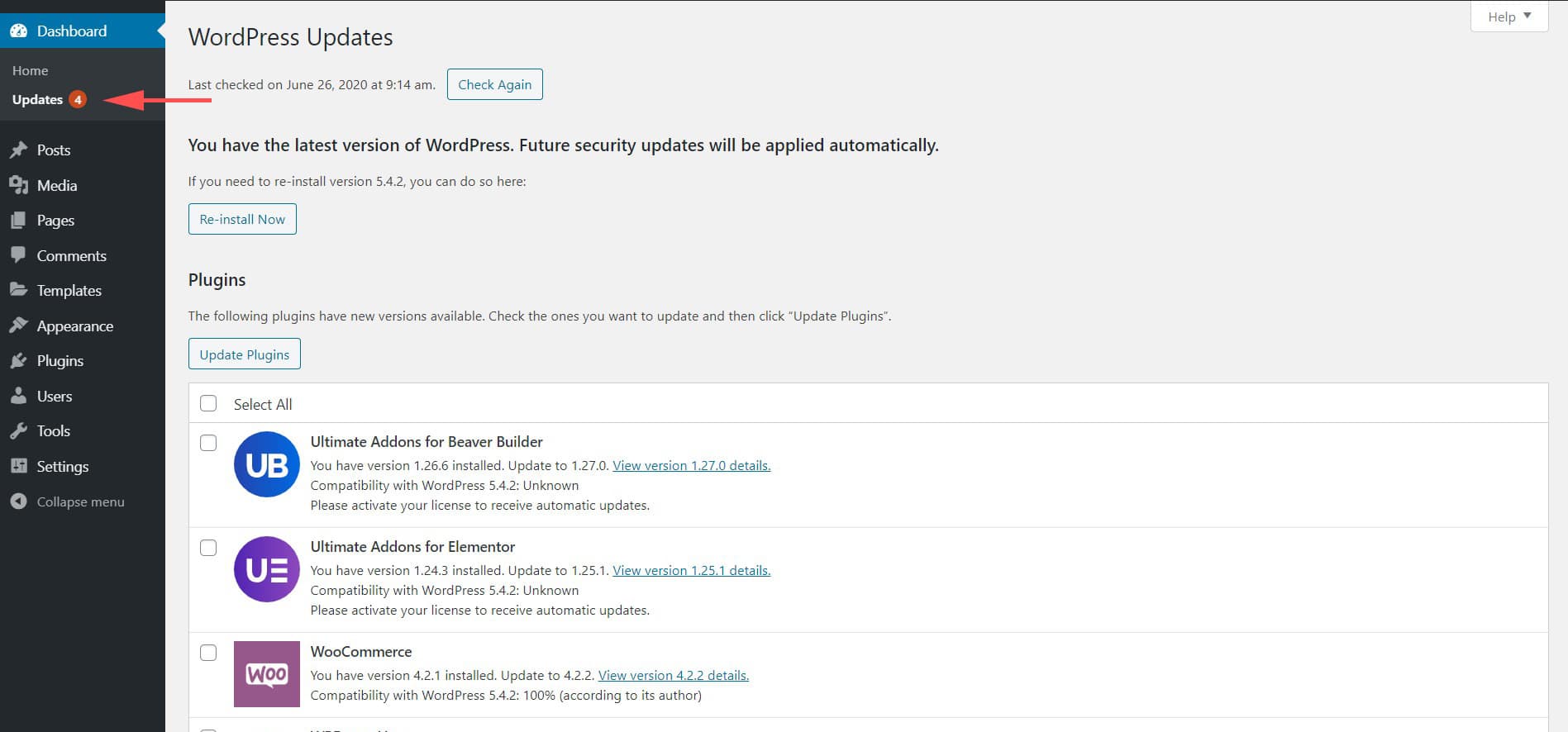
Update Your WordPress and Reset Things
The first thing that you need to do after cleaning your site is to check if it up to date. You can update your WordPress from your dashboard.
By updating your WordPress, we mean updating
- Core WordPress
- Plugins
- Themes
You can choose to manually update them or through your site’s dashboard. From there, click on Updates.
Apart from updating things, you also need to reset the site’s configuration settings.
The best approach to resetting the site’s configuration settings is by doing:
- User passwords reset
- Generating new secret keys
- Reset plugin settings to default and then manually reconfigure them
Harden WordPress by Installing Security Plugins
Hardening WordPress means making your server and WordPress site more secure. We recommend security plugins such as MalCare, WordFence or Sucuri, to harden your site.
We have a detailed guide on how to harden WordPress site which you can check here.
Create Backups
Backups can play a key role in helping you restore your site when it is hacked. You can use backup plugins to create a good backup schedule.
We recommend you to read our backup WordPress site guide on how to create and manage backups.
Do Local Computer Scan
There are some chances that your local computer can be infected too. For example, your computer might have a keyboard tracer that logs every single keyboard input and sends it to a remote server. This can leak critical info such as your website login name and password.
That’s why you need to scan your local computer with an antivirus program.
Use Firewall Plugin
The last step is to use a firewall plugin and protect your site from external threats.
You can use Cloudflare, Sucuri or JetPack to secure your site.
Remove Malware Warnings
The last step in fixing your hacked WordPress site is to remove malware warnings. Generally, once your site gets infected, it is blacklisted by entities such as McAfee, Google, and so on!
That’s why you need to ask for a review once you think that you have cleaned your WordPress site.
The process for asking for a review depends on the nature of your hack. That’s why you need to go through the Request a review article by Google.
What’s Next?
There is no doubt that no one wants their website hacked. But, even if it hacked, as you can see, there are plenty of ways you can restore it.
If you are a newbie or do not have technical knowledge on how to handle WordPress, then it is wise to go with any of the professional service providers.
All the services that we discussed in this article, MalCare, Sucuri, and WordFence, offer urgent plans that can help you get your site up and running in a matter of hours.
For those who either do not have the budget or want to fix the site themselves, can use our DIY guide for fixing hacked WordPress sites.
So has your website ever been hacked in the past? Share your experience in the comments below, and it might provide some insight to your fellow readers.

Pratik Chaskar holds the pivotal role of CTO at Brainstorm Force, serving as the backbone of the company. Renowned for his organizational skills, strategic thinking, problem-solving attitude, and expertise in leading and executing plans, Pratik plays a crucial role in the BSF’s technological landscape.
Disclosure: This blog may contain affiliate links. If you make a purchase through one of these links, we may receive a small commission. Read disclosure. Rest assured that we only recommend products that we have personally used and believe will add value to our readers. Thanks for your support!





Thanks! for putting up such a helpful article..Though I already use plugin, it’s really interesting to read DIY section 😉
Keep it up!
You’re welcome! 🙂